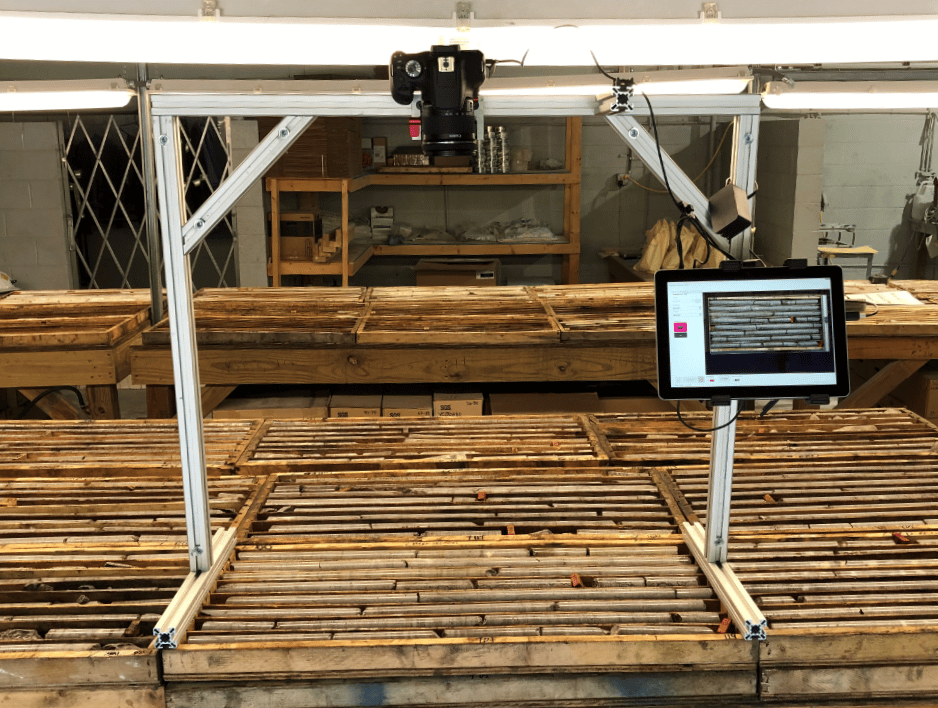
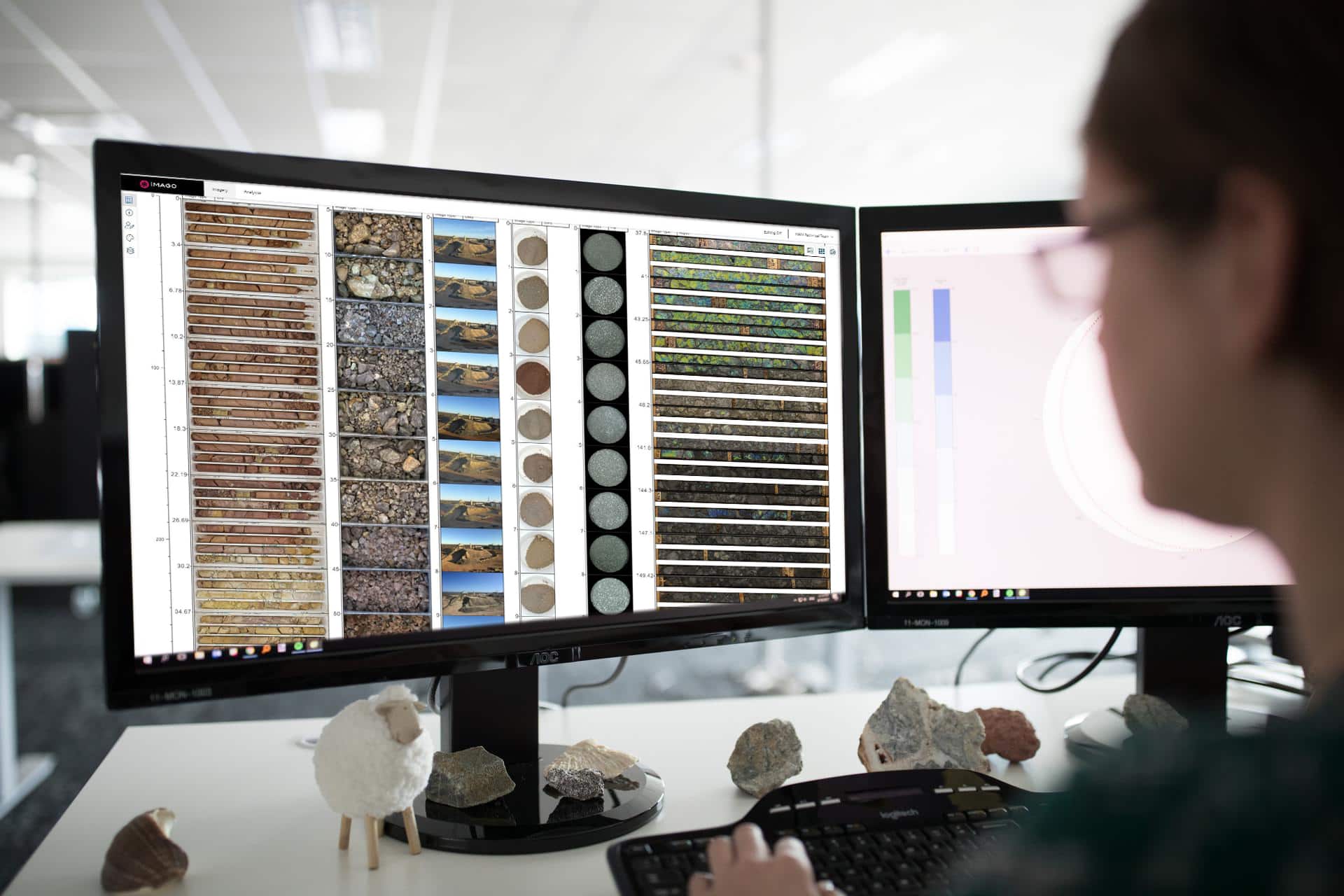
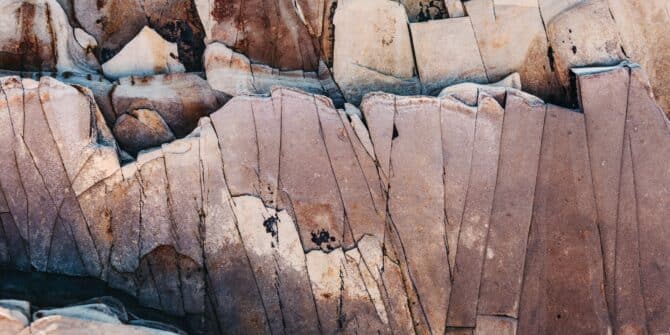
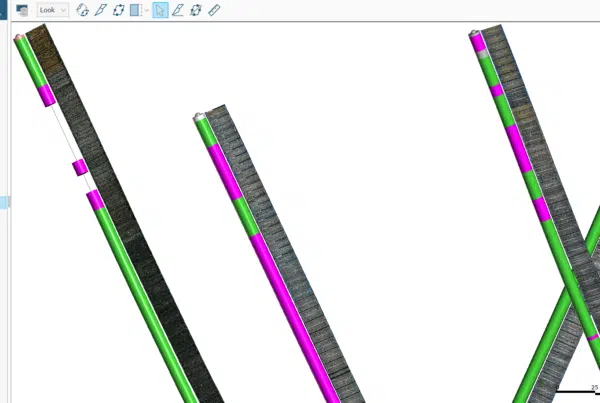
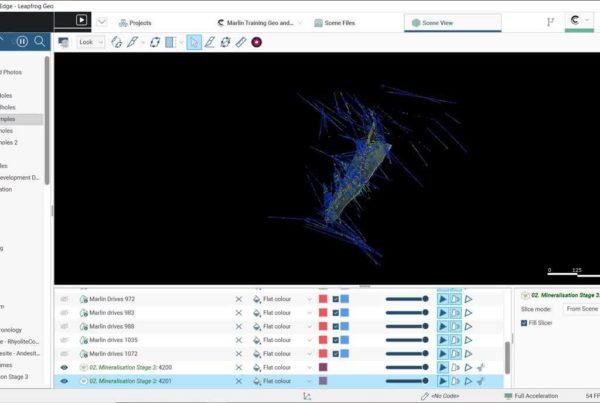
Imago streamlines your core logging process and saves time by enabling you to capture consistent, high-quality images of your drillhole core. The fast, intuitive, and easy-to-use interface means more time can be spent on the tasks that matter.
Imago controls your camera, captures the images for you, and automatically transfers them to your laptop or PC meaning no more manual handling of your core imagery.